Ransomware poses a unique threat in the digital world. Large organisations were used to the idea that hackers would try to steal their data to be sold on the dark web. They optimised their cyber defences accordingly, or didn’t consider themselves vulnerable if their data was not valuable to cyber criminals.
Ransomware turned this idea, and complacency, on its head. The hacker doesn’t target an organisation because its data is valuable to others, but because it needs its data for its own functioning. The hacker doesn’t try to steal the data, or move it anywhere; it remains on the victim’s system/network but in an encrypted and inaccessible form. The hacker is not interested in selling the data to any 3rd party, but holds it to ransom and uses it to extort payment from the victim.
Why Are Public Institutions Vulnerable to Ransomware?
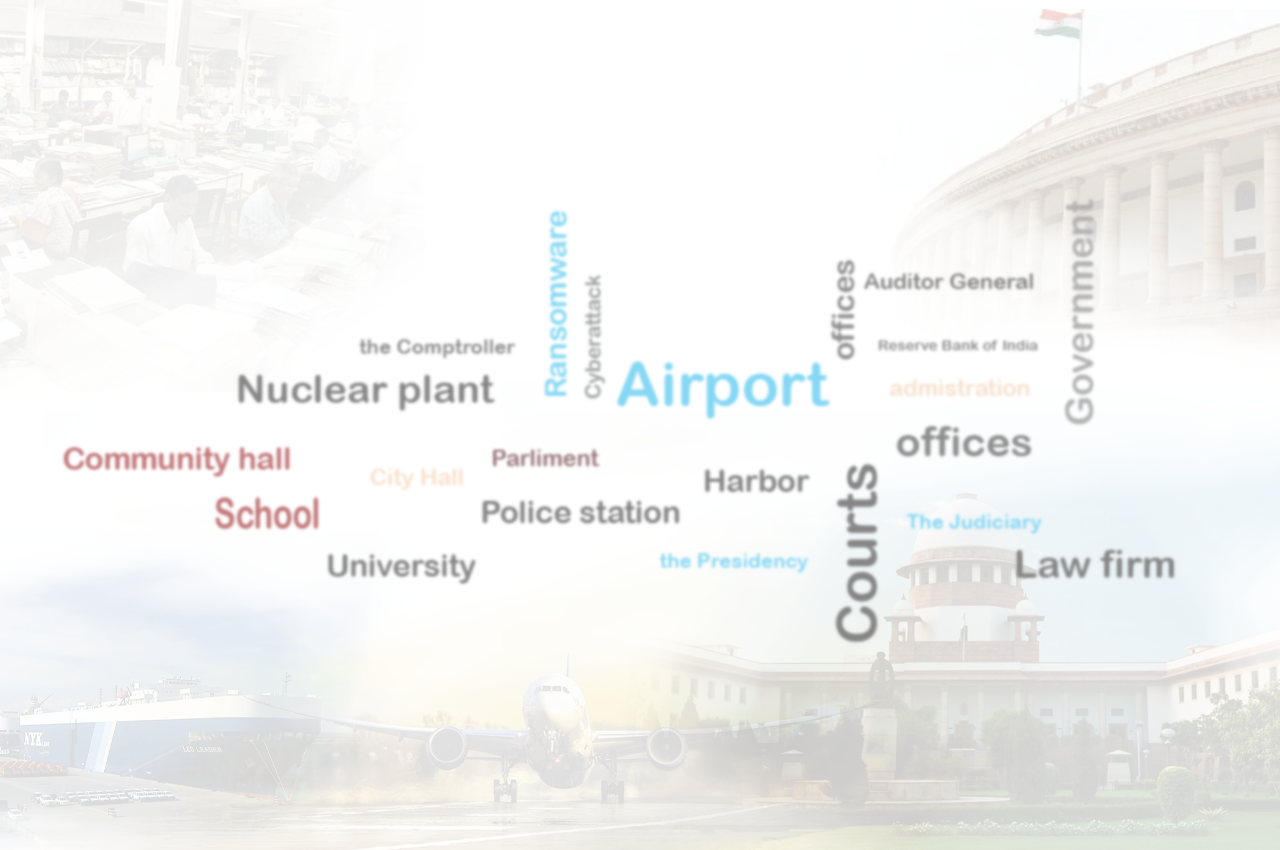
There is no denying that municipalities, local government, or public sector services in general, are more vulnerable to cyberattacks. The news is filled with stories of ransomware attacks on public institutions. An attack can have widespread impact and affect critical services.
In the US, the cities of Atlanta and Baltimore have been high profile victims of ransomware, but smaller towns have not been spared: Lake City has a population of around 12,000 and paid $460,000 in ransom to regain control of its systems. Courts, hospitals, and airports have been hit by ransomware.
Closer to home, one of the terminals at the Jawaharlal Nehru Port Trust had its operations disrupted by the GoldenEye ransomware. The WannaCry ransomware affected the corporate affairs ministry’s MCA21 portal and the Andhra Pradesh police.
There are several reasons why public institutions are more vulnerable to such attacks:
- They deal with a lot of data – Government services maintain a lot of records for a long period of time, which are essential to their functioning, which makes it easier to disrupt their operations by making the data inaccessible
- They provide essential services – This brings a lot of pressure from society on them to quickly restore the services, which increases the chances of them paying the ransom
- They are public facing – Providing public services means they have to provide access to many people, including citizens, other government departments, contractors, etc. This greatly increases the attack surface making the network easy to infiltrate, and the ransomware can also spread easily within the network
- They partner with others – Government bodies partner with the private sector, and cyberattacks on the partners can impact them. In the case of the Jawaharlal Nehru Port Trust, the affected terminal was operated by AP Moller-Maersk. 17 of its terminals around the world were impacted by the ransomware attack.
- Their IT budgets are limited – Constrained resources, especially in smaller public institutions, make securing and upgrading systems and networks difficult. Restricted budgets also limit cybersecurity training for users. Both of these make it easier to breach their defences
How Can Such Ransomware Attacks Be Prevented?
Ransomware infects and spreads through the victim in a variety of ways. The precautions to be taken against ransomware are similar to precautions against other cyberthreats.
- Password Hygiene – Default passwords, easy-to-guess passwords, password recycling, and infrequent password changes all contribute to system and network vulnerabilities. Create a strict password policy and enforce it. You can find tips to create strong passwords here. Passwords hygiene should be enforced on all devices, not just user devices i.e., servers, routers, etc. should all have strong passwords
- Install patches – Many successful ransomware attacks have been carried out by exploiting vulnerabilities that were patched long ago, but the patch had not been applied in the victim’s machine – it takes just one compromised machine to provide an entry for ransomware, after which it can spread throughout your network. Just like passwords, patches should be applied for all devices
- Avoid Default Ports – Using default listening ports for services like RDP can leave you open to ransomware. Reviewing and changing ports that are used adds an extra layer of security your IT ecosystem
- Upgrade systems – Older devices, software, and operating systems that are no longer supported by their vendors may not receive the latest patches to protect them from cyberattacks. Implementing a plan to identify and replace such IT assets is necessary to stop ransomware
- Anti-Spam/Phishing – Spam/phishing emails can also be used by cyber criminals to breach your defences and deploy ransomware. Social engineering is used to trick a user into clicking on a malicious attachment or link which launches the attack. Educate users not to open attachments or links that are suspicious or from unknown users, and block unauthorised software installations. Anti-spam/phishing tools should be a part of your defences
- Regularly Backup Data – Ransomware works by encrypting your data. If you regularly backup your data, you can restore it from a backup and restart operations without trying to decrypt data or resorting to paying the ransom. This requires a good backup plan to ensure you don’t backup and restore compromised data. You may also need to consider data sovereignty if your organisation handles sensitive data. You can find the building blocks of a good data backup strategy here
- Use Cybersecurity – Protect your organisation’s data with a cybersecurity solution that is known to be effective against ransomware, such as K7 Endpoint Security for Business
- Educate Users – The well informed user is a critical part of your cyber defence. Provide users with training on using cybersecurity tools, spotting a cyberattack, identifying phishing campaigns, etc.
Public institutions may be a very attractive target for ransomware attacks but the reasons that make them more vulnerable to them apply to many private sector organisations as well. Neither category needs to be vulnerable to ransomware. The above steps can help mitigate such threats and, as a bonus, will be useful in recovering from data loss due to non-malicious events such as hardware failure.