The Lazarus APT group, believed to be sponsored by North Korea, is no stranger to us. The infamous group is now planning a large scale attack by leveraging the financial and medical anxiety over COVID-19.
Cyberattacks that exploit the pandemic are no longer new. This time, however, we have advance information of a significant cyberattack. News has emerged that the Lazarus group is launching phishing attacks against multiple counties that have announced significant financial assistance to their citizens in the wake of COVID-19. India is one of these countries.
How Does the Attack Work
Adversaries have used the most famous method – the phishing attack. This is a form of social engineering where the goal is to mislead the victim into believing that the message, link, or file is genuine and that they should perform an action which is harmful to their interests.
Many countries across the world have announced various forms of aid to their citizens and businesses. Therefore, an email that claims to be from the government offering fiscal aid could be mistaken for a genuine email by a victim. This is the technique utilised by the Lazarus group. Let us examine an email targeting Indians:
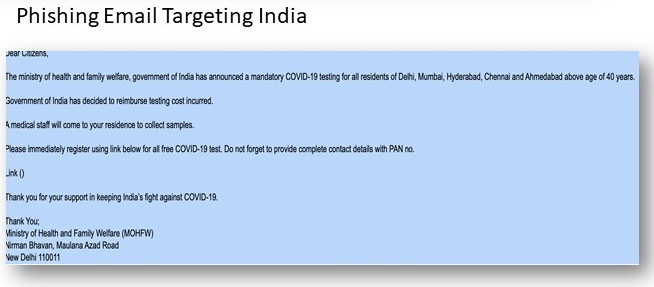
Image Source: CYFIRMA
The email references a government ministry and COVID-19 testing, names of specific cities, and an age limit. These form an attempt to add credibility to the email.
The email offers to reimburse cost of testing. This exploits two causes of anxiety to the victim: the fear that they might have COVID-19 which is addressed by the test, and the cost of the test which is addressed by the reimbursement offer. Both of these may be sufficiently persuasive for an anxious person to fall victim to the cyberattack.
The attack itself requires the victim to register for the test at a link, where they will have to divulge a great deal of personal information about themselves including their PAN number. This information, once harvested by the attacker, sets the stage for identity theft. The attacker, or whoever the attacker sells the data to, can pretend to be the victim to perpetrate a wide range of scams for which the victim will be held responsible, or steal directly from the victim.
How Do We Know That The Email Isn’t Genuine?
There are several factors based on which we can identify that the email is malicious:
- If such a scheme is launched by the government, it would have been heavily publicised through traditional media like newspapers and television. It is very unlikely that an email would be the first indication of such an initiative. When in doubt, verify with an internet search
- The email does not refer to any government order, law, mandate, or scheme name. This is highly unusual as official communication from the government will always provide such details for reference
- The Ministry of Health and Family Welfare, Government of India as spelt as ‘ministry of health and family welfare, government of India.’ Similarly, the abbreviation is given as MOHFW instead of MoHFW. Such incorrect capitalisation immediately reveals that the email’s origins are suspect
Is India the Only Country Targeted?
No, 6 countries including Japan, UK, USA, India, Singapore and South Korea have been targeted.
The Lazarus group appears to have 2 million Indian email IDs to spread their attack in India. While this may appear to be a small proportion compared to the size of the Indian population, it is still large enough to inflict significant damage if many of their targets fall victim to the attack.
Details of attacks against the other 5 countries can be found here.
How Can We Protect Ourselves Against Such Attacks?
Follow these steps to stay safe from this and many other phishing attacks:
- Be sceptical. If the email sounds too good to be true, it is most probably a scam. If you haven’t heard about the scheme or offer through any other source, it may be an attempt to defraud you
- Check the sender’s email ID, especially the domain name (the portion after the ‘@’ symbol). Phishing emails often have domains that are very similar to legitimate IDs but even a slight difference is enough to identify a fake. Check the website of the organisation that the email is supposedly from to see if they have listed email IDs with the same domain name used in the email. Note that email IDs can be spoofed, so this check does not, by itself, prove that a message is genuine
- Check the language used in the email. Obvious spelling and grammatical errors are a sign that the email isn’t from an official source
- Verify if you have ever used that email ID to register with that government agency before. If you have not, then it is unlikely they would have your email address
- Check with others whom you know if they have received such a message
- Do not click on any attachment or link, or perform any action required in the email, unless you are sure that it is genuine
- Use a cybersecurity product like K7 Total Security that is constantly updated to protect users against the latest phishing attacks











