There is a reason why Cybercriminals often snare their victims using old and widespread malware and techniques. Instead of designing a malware or attack technique from scratch, they prefer renovating cracked, or open-source modules to achieve better results. Steganography is such a notorious abiding technique, frequently used by the adversaries in many sophisticated cyber-attacks to fly under the radar.
What is Steganography?
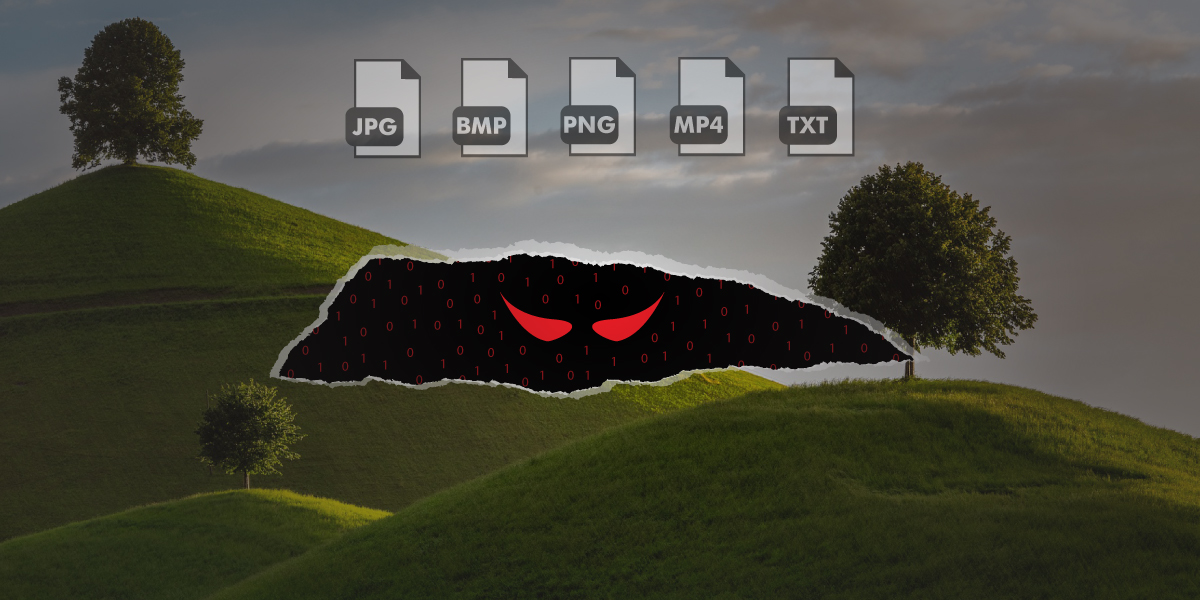
Steganography is neither malware nor a social engineering technique. Instead, it comes handy to the adversaries while executing a sophisticated cyber-attack. The method helps them hide malware and other important attack information into innocuous-looking system and user files.
Adversaries could overwrite a random image, video, text, or message file to inject malicious information, code, or something identical through steganography techniques and tools, without arising suspicion. The steganography technique helps them to encrypt the data before inserting it in a target file to stay inconspicuous.
[Read More: The K7 Cyber Threat Monitor Q1 2020-21: A Snapshot Into The Countrywide Threat Landscape]
Steganography vs Cryptography
Though steganography and cryptography sound quite identical for the operation style, they are quite different in principle. While the cryptography technique involves just encrypting or decrypting a certain amount of text using a cypher code, the steganography process is responsible for hiding the data and manipulates encryption as a part of the entire process.
The steganography technique often utilised for hiding sensitive information, including cyber-attack related instructions to obscure the malware content and keep the Command and Control (C2) server information in disguise.
How Steganography works
The steganography technique also lets the threat actors utilise the unoccupied portion at the end of a file to append the malware payloads or related information. The method often helps them hide the malware existence from any cybersecurity software.
While using the steganography process, the attackers ensure the infected file quality maintains the same size to stay out of suspicion.
The complexity of the stenography process also manipulates the limitations of the Human Auditory System (HAS) or Human Visual System (HVS) while embedding data.
[Read More: Social Engineering And The Psychology Of Falling Prey To Cybercriminals]
How does steganography work in an image file?
The technique of embedding malicious information into an image usually gets done via Image Domain or Frequency-domain methods.
The technique used in the Image Domain technique alters the embedding technique in compliance with the image file’s pixel arrangement sequence. The method manipulates specific pixels’ colour value to ensure a typical user could never find any difference between the source and the malicious image file. The Image Domain technique often gets used in files having lossless format.
The Frequency Domain technique or Transform Domain technique could get applied to any image formats, including lossless. The method involves several tools and algorithms to embed the text by transforming DCT and Wavelet. The technique sometimes tweaks the colour luminance of the image file.
Digging deeper
In image-based steganography, the adversaries often manipulate various property information such as image luminance, chrominance, etc. A few steganography techniques even manage the pixel relations of an image file via colour palate sorting, increasing image noise, or tweaking the colour indexes.
Adversaries keep the element size relative to the size of the target image file. The technique also makes sure that the image element and the embedded data, both would get unaffected if the image file gets rotated, blurred, adjusted for noise, sharpened, scaled, or goes through other linear or non-linear filtering process.
[Read More: Everything You Should Know About Phishing]
Other Steganography varieties
Alongside images, the steganography technique could get used on the file formats mentioned below:
Text Steganography
A con artist can hide certain pieces of text through tweaking chunks of text or generate readable versions of the source file via text steganography. The method uses format based, random, statistical generation, and linguistic-based processes.
Audio Steganography
An adversary can also hide elements inside an audio file via least significant bit encoding, parity encoding, phase encoding, and spread spectrum. In the process, the hacker conceals the text inside audio signals by modifying the binary sequence of it.
Hiding elements inside a digital audio file such as mp3, wav, or WMA is a complicated task. However, there are numerous tools available on the internet, which can help you hide your data through a few clicks.
Video Steganography
For hiding a significant chunk of malicious data, hackers often utilise video steganography tools. The video streaming process usually manipulates a series of audio and image streams together. And a video steganography tool could insert data into each image and audio stream without affecting the file size much. This steganography technique could hide a massive amount of data and popular among the intelligence agencies.
Network Steganography
Adversaries manipulate tons of steganography tools available over the internet to hide data inside network packets. In this process, they encapsulate a stream of data inside the header or any other optional field of a TCP/IP packet.
How to detect steganography based malware
Identifying a malware injected steganography file could be extremely difficult because most of such data hardly prompt any difference from the original record. A few steganography manipulated malware detected in the recent past. And several government intelligence agencies, threat actors, and cybercrime gangs are developing more complex steganography techniques to make it harder to identify.
However, you can use any decent analytical tool to detect a steganography infected file. Alongside you should also ensure installing a stable multi-layered cybersecurity solution software such as K7 Enterprise Security on your system to identify the malware as soon as it surfaces.