The proliferation of Ransomware multitudes year-over-year and shows no sign of stopping anytime soon. Its wrath has brought many public/private enterprises and SMBs to their knees for a massive ransom and disruption. Besides targeting prime industries with malicious vectors, many ransomware actors have also transformed it into a high-paying revenue model by offering it as a service.
RaaS in easy words
Putting in the software as a service (SaaS) or platform as a service’s (PaaS) shoes, ransomware as a service (RaaS) offers an interactive package. A typical RaaS service includes a well-etched interface, a dashboard to control the entire operation, a ransomware vector, and often a helpline, user reviews, and forums.
RaaS operators offer their services in three different business models- timely subscription, lifetime license, and affiliate program.
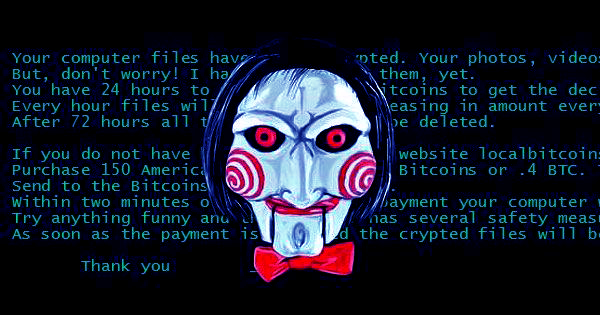
Jigsaw Ransomware as a service custom message
Subscription Model
The subscription-based RaaS service works just like any other SaaS or streaming service. The operator (often, a group of malware authors) offers its ransomware-related service for a limited period in exchange for a mentioned price in BitCoin, Ethereum, and other popular cryptocurrencies.
Lifetime Licensing
Operators offering a lifetime licence provide fully loaded ransomware kits and require malicious tools to execute the menace. These services are way more expensive than their subscription-based counterparts.
Read More: Sodinokibi Ransomware And QBot Malware: The (R)Evil Connection Explained
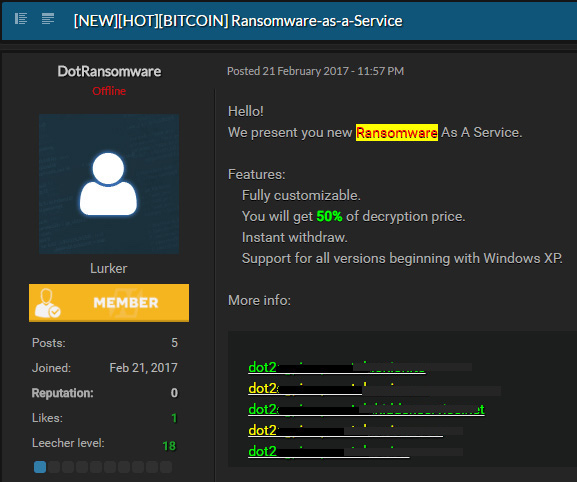
The Affiliate Model
These operators offer affiliate programs and often publish advertisements on the dark web. On this model, the affiliates are often experienced with malware kill chains but sometimes have zero exposure. In such attacks, the affiliates choose the victims, execute the operation with the operator’s help, and pay roughly 20-30% of the ransom. Sophisticated RaaS services automatically collect the operator’s cut as soon as the victim pays out.
Besides, many ransomware operators partner with other malware developers and share the money according to their contribution.
Out of these four revenue models, an affiliate-based business model is more prevalent.
How affiliate based RaaS Works
Most of the RaaS models follow a standard workflow model mentioned below.
- The developer builds or refurbishes a ransomware kill chain abusing a specific set of exploits.
- Once the affiliate gets access, they update the payload hosting site with the exploit code.
- The affiliate would identify and observe the victim, determine an infection vector, and embed it on a spear-phishing email.
- Affiliates often buy additional Phishing as a Service (PaaS) to lure the target victim via emails. A typical PaaS infused email bundling malicious websites, email lists, and many hacking tools.
- Once the victim clicks on the malicious link, the target’s internet traffic automatically redirects to the rogue website.
- The website uploads the ransomware payload on the victim’s system/network.
- Once activated, the ransomware modifies the system /network to establish its reign. Later it identifies and destroys existing data backups, encrypts the target files, and determines other targets.
- Once the target files are encrypted, the RaaS dashboard sends a custom ransom note with detailed instructions.
- If the victim pays the ransom, the process would involve a money mule to forward the money to multiple forged accounts to mask the affiliate and the developer’s identity.
- If the victim fails to pay, the developer could leak the victim’s sensitive data on dark web-based websites to threaten the business integrity.
- Once everything gets sorted, the affiliate sometimes delivers the decryptor program to the victim.
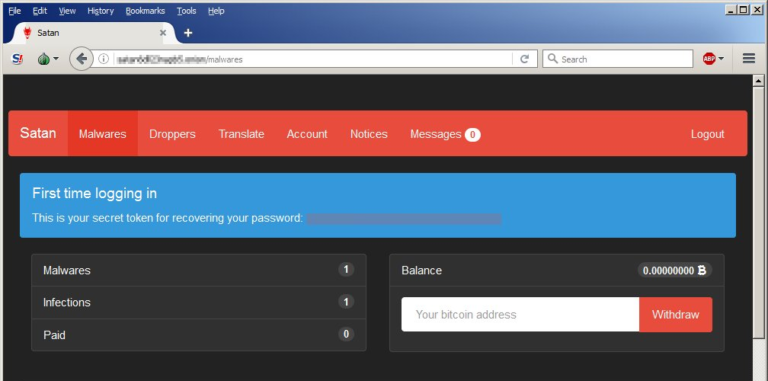
Satan ransomware as a service
Infamous RaaS families
Dark web offers a plethora of RaaS like StamPado, RaaSBerry, Frozr Locker, DiamondFox, Sodinokibi, Satan and more on several marketplaces. And their price differs according to their level of sophistication.
These groups often have hundreds of affiliates worldwide and make billions of dollars every year. For instance, GandCrab affiliates extracted roughly $2 billion in extortion payout from its victims in its fifteen months of existence. Before disappearing in October 2019, GandCrab developers asserted that their average weekly earnings were roughly $2.5 million. Though disappeared, multiple malware strains and coding patterns have determined that the group has reincarnated as Sodinokibi. The RaaS service offers a customized solution to its affiliates.
Ryuk, Phobos, Smaug and Dharma are other significant RaaS operators. Smaug offers customized ransomware solutions according to victims operating systems, including Windows, macOS, and Linux.
Notorious RaaS operator Ryuk which has victimized many state and local governments, schools, universities, hospitals, and other businesses, offers a complete dashboard and enhanced customer support to its affiliates for being more interactive and user-friendly.
On the other hand, Dharma, which has remained active since 2016, has taken down a series of enterprises and SMBs located in India, Russia, China, and Japan via affiliates with amateur knowledge.
Another active RaaS Phobos gets offered in multiple avatars such as EKing and primarily targets Remote Desktop Protocol (RDP).
Adequate Safeguards
Though sophisticated RaaS mostly eyes enterprises and government bodies, a few operators still prefer small and medium businesses (SMB).
Following are the list of safeguards we strongly suggest to the enterprises across sizes and the end-users:
- Enterprises should perform asset management for all the existing computers, servers, data, software platforms, applications, and clients and maintain a strategy to allocate resources.
- Ensure disabling the macro service if any of your computers still use an older version of Microsoft Office.
- Ensure all your data gets backed up in an encrypted format regularly.
- Enterprises and SMBs should arrange necessary security hygiene seminars and webinars for all employees. In addition, the awareness campaign should offer adequate knowledge about identifying suspicious emails, social engineering attacks, shadow IT practices, and software hygiene.
- Install a robust multi-layered cybersecurity solution such as K7 Enterprise Security which offers anti-ransomware, host-based intrusion detection system (IDS) and intrusion detection software, email filter, rogue website detector, and many more.
- Install all the available patches and updates for your application software, operating system, and other installed solutions.











