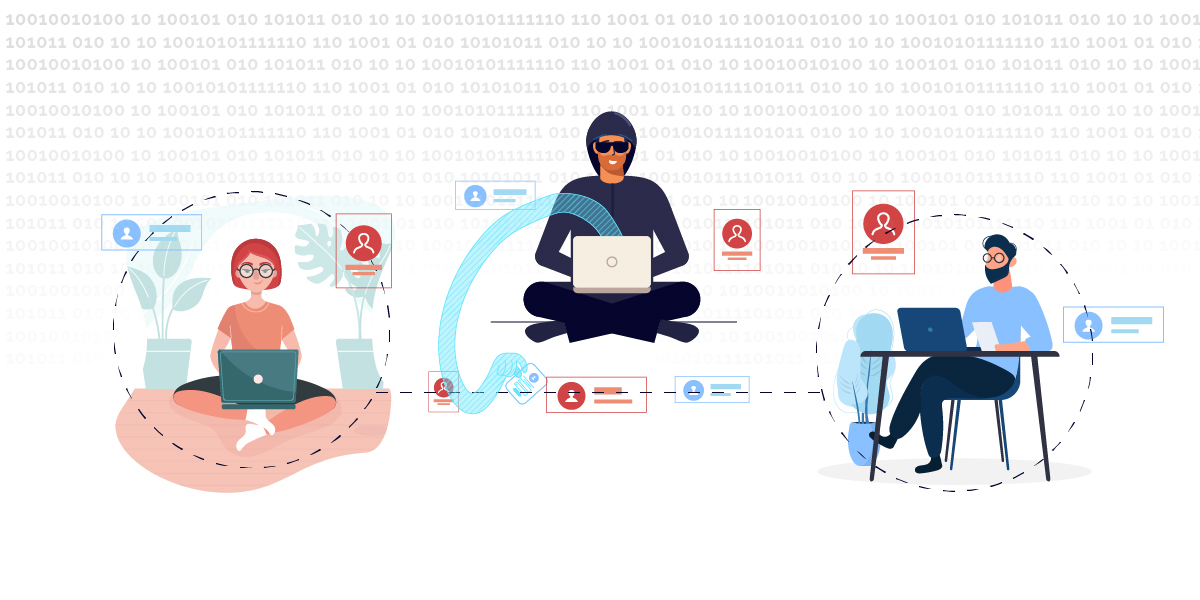
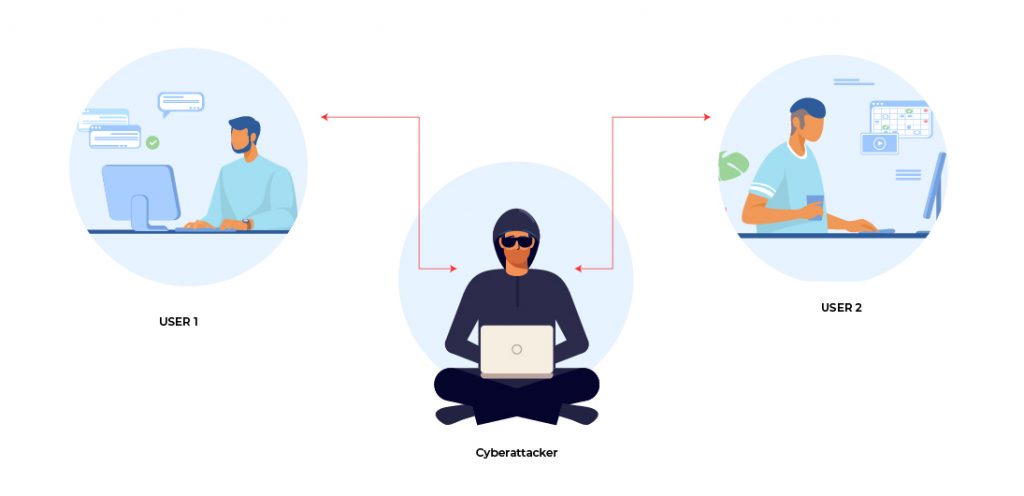
The Man-In-The Middle (MITM) cyberattack is easily understood from its name: a cyberattacker manages to insert themselves as an intermediary in the exchange of data, with consequential impact on data security and integrity.
How Man-In-The-Middle Attacks Work – A Real-world Example
- An employee is chatting with their boss through an unsecured Wi-Fi network
- The boss informs the employee to urgently transfer an amount to a specified bank account number
- A hacker intercepts this conversation and changes both the amount and the bank account number in the message that is received by the employee
- The employee performs the transaction and sends a message to the boss confirming that the amount has been transferred to the bank account number
- The hacker changes the amount and account number back to the original data before the confirmation message reaches the boss
- By using this MITM cyberattack, the hacker is able to steal funds from the organisation without arousing suspicion while the attack is in progress
It should be noted here that MITM attacks need not be limited to digital interaction between humans. Communication from and to machines, and even between machines, may also be intercepted e.g., IoT devices may be compromised by MITM attacks to carry out industrial espionage or sabotage by either modifying the data they report or the instructions they receive.
Prevalence of Man-In-The-Middle Cyberattacks
Is your organisation really at risk from an MITM attack? 95% of HTTPS servers are vulnerable – that’s an alarming statistic. Here’s another one: 35% of exploitation activity involve MITM attacks. These cyberattacks may not be as famous as ransomware or phishing, but they represent a prevalent and significant threat to enterprise cybersecurity.
Types of Man-In-The-Middle Attacks
Common Man-In-The-Middle attacks include:
Malicious Wi-Fi
We have already discussed this in the real-world example above. Compromised Wi-Fi networks are a popular choice amongst cyberattackers because such attacks are relatively simple and easy to deploy. Having secured Wi-Fi within your organisation is not enough to protect your employees as they may use W-Fi on their laptops outside the organisation e.g., in a coffee shop – except that the Wi-Fi network they are using doesn’t belong to the coffee shop; it is a malicious hotspot created by an attacker who is also present in the coffee shop posing as a customer. Enterprise cybersecurity solutions such as K7 Endpoint Security can control which Wi-Fi networks the laptop can connect to, but employees may also use their personal devices for communicating with colleagues which may still expose the organisation to an MITM attack.
Adware/Malware
It may be hard to believe that an application bundled with computers by the OEM could be considered unsafe, but that is what happened with the Sailfish adware. Ostensibly a visual search tool, the bundled application acted as an MITM attack to inject ads into websites visited by the user and also used the same encryption key for all computers that had the adware installed which opened the doors to severe cyberattacks from threat actors. Any program that attempts to modify the content of web pages before they are viewed by the user can be considered an MITM attack as they can be used for more alarming purposes than injecting ads. Malware that can step into digital communication channels pose the same threat and may enter a device through malicious attachments, infected USB drives, software or hardware vulnerabilities, and attack websites.
Man In The Browser
This variant of MITM specifically targets the victim’s browser e.g., through a malicious browser extension. The extension allows the attacker to monitor and compromise all browser-based activity which is a significant portion of an employee’s tasks as many organisations now use internal websites or cloud-enabled solutions for commercial and administrative operations.
ARP Poisoning
Address Resolution Protocol (ARP) Poisoning (or ARP Cache Poisoning) modifies the IP address associated with the MAC address of a device. In layman’s terms, it means that a hacker can insert themselves between an endpoint and router (for example) and pretend to be the router to the endpoint and pretend to be the endpoint to the router. All data traffic that is meant to flow between endpoint and router will now pass through the hacker’s device.
DNS Spoofing
The Domain Name System (DNS) is used to link the human readable website name (domain name) to its IP address. As it would be inefficient to look up the DNS records every time for every website, the DNS server stores this information in a cache. By poisoning the cache, an attacker can link an incorrect IP address to the website’s domain name and direct traffic meant for the website to the attacker’s own malicious website. This could be used to harvest login credentials, access proprietary data, or spread incorrect information.
IP Address Spoofing
IP Address Spoofing replaces the source IP address of a data packet with a forged IP address. An attacker can use this technique to compromise devices or networks by making them believe they are connecting to a trusted device.
SSL Stripping
Also known as a downgrade attack, this technique forces a browser to connect to a website using HTTP instead of HTTPS i.e., the connection is no longer encrypted and is therefore open to data theft and data manipulation. This attack requires the initial connection request to be sent via HTTP (e.g. clicking on a link that was created before the website was upgraded to HTTPS) to which the website will respond in HTTP to redirect to HTTPS. The attacker inserts themselves during the HTTPS redirection process, communicating with the website via HTTPS and the victim’s device via HTTP to receive information sent by the victim to the website in unencrypted form.
K7 Security provides robust, multi-layered Endpoint Security and Unified Threat Management to protect your organisation’s endpoints and network. Contact us for more information on how we can help protect your IT ecosystem against cyberattacks.